Dealing with concerns over exposure to harm
In the race towards the Internet of Things, some businesses are being left behind. In particular, companies that focus on critical supply chains have too much to risk by opening up their systems to the Internet. For them, one compromised machine could mean that the food, pharmaceuticals, energy, water or critical supply that millions depend on might be tampered with and subsequently destroyed. Or worse, the products actually evade detection and are introduced into the public supply.
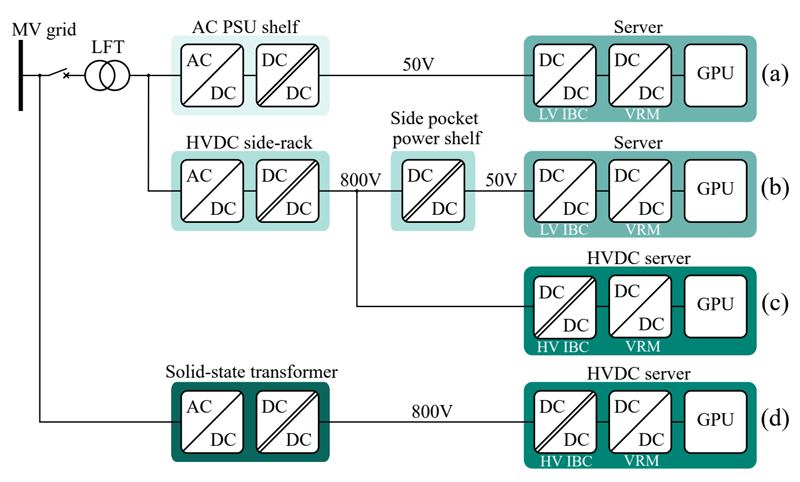
All of the gains that could be provided by the Enterprise IoT (EIoT) are not enough for many to overcome the severity of these risks of exposure to harm. This means the productivity gains that can be realized by a connection to the resources (people and machines) in a plant can be achieved only if properly implemented in a manner that addresses their needs (see Figure 1). As a result, the processes needed to drive performance (like Six Sigma) are only as good as the systems that can be put into place to monitor processes and supply chains and the data that can be collected.
Click image to enlarge
Figure 1: Any IoT solution must address business needs
Disruptions create instability
Plant responses are delayed, and operations end up being easily shaken, by disruptions in supply and demand. To overcome the stability problems, companies resort to larger plants and batches that rely on fixed resources which lead to generic products, warehousing and distribution issues.
Large plants with fixed installations turn into more expensive fixed machinery, and integration costs that are becoming a larger part of the plant cost. ROI is measured in years, if it even happens.
If the data available through the EIoT were made securely available to these supply chains, it is easy to see how improvements could quickly be made with regard to efficiency, reliability, and employee safety.
How then can the risks related to deploying EIoT be eliminated? There are steps that can be taken to address these issues.
Security
Get your network away from the well-known standards that are targeted, and into strategies that make security possible.
• Use wireless as part of the network media… not WiFi, but layered protocols over wireless that are too complex to hack (S99 appendix).
• Install data packages tailored by Laird so that the security of that data remains uncompromised (S95).
• Use specific hardware interfaces to secure network from common devices (like Smart Phones, etc).
Reliability
Once a business has decided to deploy the EIoT in a plant, what kind of performance can they expect from the system? Are there guarantees that they can rely on?
• Systems with a dedicated wireless backbone using multiple transmission frequencies to make sure networks are never lost.
• Site surveys to verify that coverage is complete and interference is minimal.
• FCC licensed frequencies to insure that bandwidth is available.
• Optimize hardware layers to improve data flow.
- Instead of; Machineè SCADA è MES è Plant è ERP
- Use ; Machineè SCADA / MES è Plant / ERP
Productivity
Once a network structure has been planned and the reliability of the system has been validated, interaction with machines can begin to improve data collection and empower productivity and safety.
• Minimizing the motion interactions between humans and infrastructure so that each can do what they are best at.
• Be able to Stop/Start/Monitor lines at a safe distance with remote controls
- A fork truck driver can start a moveable pallet wrapper via 13849 remote.
- A line operator can stop a jammed machine within a safe zone remotely saving time, product and money.
Safety
• Powering machines with radio based Safety MCUs to solve the integration issues that come from discrete estop installations.
• Provide machine and SCADA level mobile estops (better coverage for lines with long conveyors).
• Multiple e-stops to provide redundancy in multi user applications (like threading a web machine).
Efficiency
• Data collected on people, machinery, materials and processes can provide the insight needed to:
- Improve the quality of the product
- Increase the speed of the process
- The safe and immediate redeployment of assets in a factory with data being instantly available via wireless.
- Monitor and adjust the production time available by all assets
- Find weaknesses in your process, allowing improvements and immediate feedback.
(Not to mention doing all of this with a reasonable Return on Investment so that adoption is rapid.)
Notes:
• ANSI/ISA-95, or ISA-95 as it is more commonly referred, is an international standard from the International Society of Automation for developing an automated interface between enterprise and control systems.
• Formerly designated ANSI/ISA-99.02.01-2009, this standard is part of a multipart series that addresses the issue of security for industrial automation and control systems. It has been developed by Working Group 2 of the ISA99 committee. This standard describes the elements contained in a cyber security management system for use in the industrial automation and control systems environment and provides guidance on how to meet the requirements described for each element.
This standard has been developed in large part from a previous Technical Report produced by the ISA99 committee, ANSI/ISA–TR99.00.02–2004, Integrating Electronic Security into the Manufacturing and Control Systems Environment. The majority of the contents of this Technical Report have been included in this standard and as such this standard supersedes the Technical Report.
The ISA99 series addresses electronic security within the industrial automation and control systems environment. The series will serve as the foundation for the IEC 62443 series of the same titles, as being developed by IEC TC65 WG10, “Security for industrial process measurement and control - Network and system security.” - See more at: https://www.isa.org/store/ansi/isa–62443-2-1-990201–2009-security-for-industrial-automation-and-control-systems-establishing-an-industrial-automation-and-control-systems-security-program-/116731#sthash.JChkgeUY.dpuf